
The first half of 2013 has been very busy from a zero-day attack perspective.
In the first six months of the year, several zero-day vulnerabilities affecting widely deployed software were found to be exploited in the wild.
Most of the zero-day exploits were initially found in targeted attacks and we witnessed how much attackers are willing to invest in these attacks when sophisticated zero-day exploits bypassed modern security mechanisms in software. In this article, we'll look at these zero-day attacks and give suggestions that can lower your risk of becoming a victim.
(point in time when zero-day attack became publicly known)
2012-12-17
MS Internet Explorer
CVE-2012-4792
2013-02-07
Adobe Flash
CVE-2013-0633
CVE-2013-0634
2013-02-26
Adobe Flash
CVE-2013-0643
CVE-2013-0648
2013-05-01
MS Internet Explorer
CVE-2013-1347
2013-01-10
Oracle Java
CVE-2013-0422
2013-02-13
Adobe Reader
CVE-2013-0641
CVE-2013-0640
2013-02-28
Oracle Java
CVE-2013-1493
2013-06-11
MS Office
CVE-2013-1331
After a
substantial jump in 2009,
The number decreased slightly from 2010 to 2011 before another
substantial jump in 2012. Although vulnerabilities affecting mobile applications
and operating systems represent a relatively small
percentage of total disclosures (projected at just
over four percent in 2013), we have seen the total
number of disclosures increase significantly.
The majority of vulnerabilities that the
X-Force team
documents are those in web application programs,
Such as Content Management Systems (CMS).In the first half of 2013, 31 percent of vulnerabilities that were publicly reported are what we categorize as applications used on the World Wide Web. This number is down significantly from 2012 where we saw levels at 42 percent. More than half of all web application vulnerabilities are cross-site scripting.
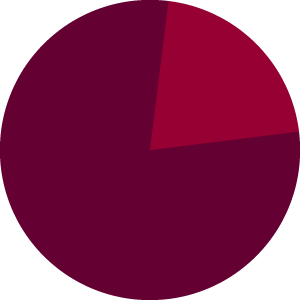
Patched : |
Unpatched : |
Patched : |
Unpatched : |
Content Management Systems are some of the most popular software used on the World Wide Web. Major CMS vendors have embraced security and do a good job of patching their core software when security vulnerabilities are reported to them.
Seventy-eight percent of all vulnerabilities reported in CMS were patched in the first half of 2013, while in 2012 we saw that only 71 percent of vulnerabilities were patched. Year over year we see that these vendors are doing a better job of keeping their products up to date.
However, third-party creators of plug-ins for CMS did not fare as well with only 54 percent of vulnerabilities having a patch supplied. With over 46 percent unpatched vulnerabilities, third-party plug-ins become attractive opportunities for attacks to occur.
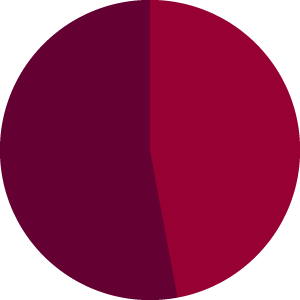
To measure the IPv6 deployment for websites, we
have done DNS requests,
which check for an AAAA
record in DNS, for millions of hosts every week. As
IPv4 is running out of space, we expect that more
and more Internet sites are switching to IPv6. We
have focused our analysis on the 100,000 most
popular and most used websites61 to see how many
of them have already stepped into the IPv6 world
are providing IPv6 up 1.2 percent.
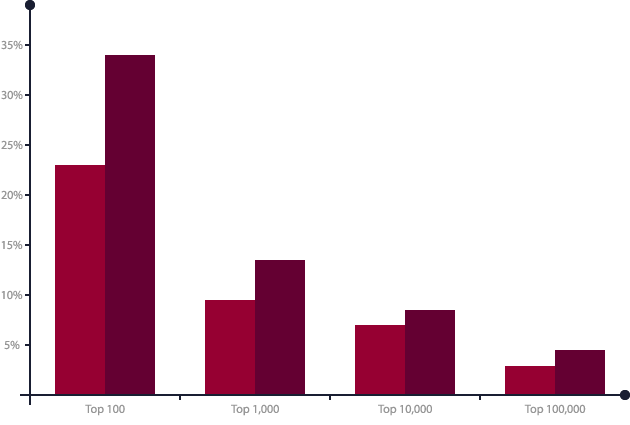
December 2012 |
June 2013 |
The IBM spam and URL filter database provides a world-encompassing view of spam and phishing attacks.
The content team has identified numerous advances in the spam and phishing technologies that attackers use. Currently, the IBM spam filter database contains more than 40 million relevant spam signatures. Each piece of spam is broken into several logical parts (sentences, paragraphs, and so on). A unique, 128 bit signature.
Each day there are Each day there are
approximately one million new, updated, or deleted
signatures for the spam filter database. The
updates are provided every five minutes.
This topic addresses the following topics:
- Spam—country62 of origin trends
- Scam/Phishing targets by industry
India |
Vietnam |
USA |
When looking at the countries that sent out the most spam over the last two and a half years, some interesting long-term trends become visible.
• Belarus is the new star with spam, sending out 10
percent in the second quarter of 2013.
• In the first quarter of 2013, the USA took over the leadership
position by sending out 12 percent, but then
declined to about 8 percent in the second quarter.
• In the first half of 2013, Spain reached the top
three for the first time in years.
• While India dominated the scene at the end of
2012, and sent out more than one-fifth of all spam
in the third quarter of 2012.
• Argentina and Italy reached the top five and top six
positions for the first time in years.
• Saudi Arabia did not repeat its performance of the
third quarter of 2012 in sending out spam and
remains flat at around 1 percent.
In practice, enabling vulnerability management with
additional contextual data
will require it to be seamlessly integrated with a security intelligence system.
Both a real time and an historic view of
network activity, including what the current threat
environment looks like and what the status is of
current security controls.
For more information please visit:
Did you know that 67 millions of content are shared each week? Why not share one of them...